Rating: 4.0
### blink
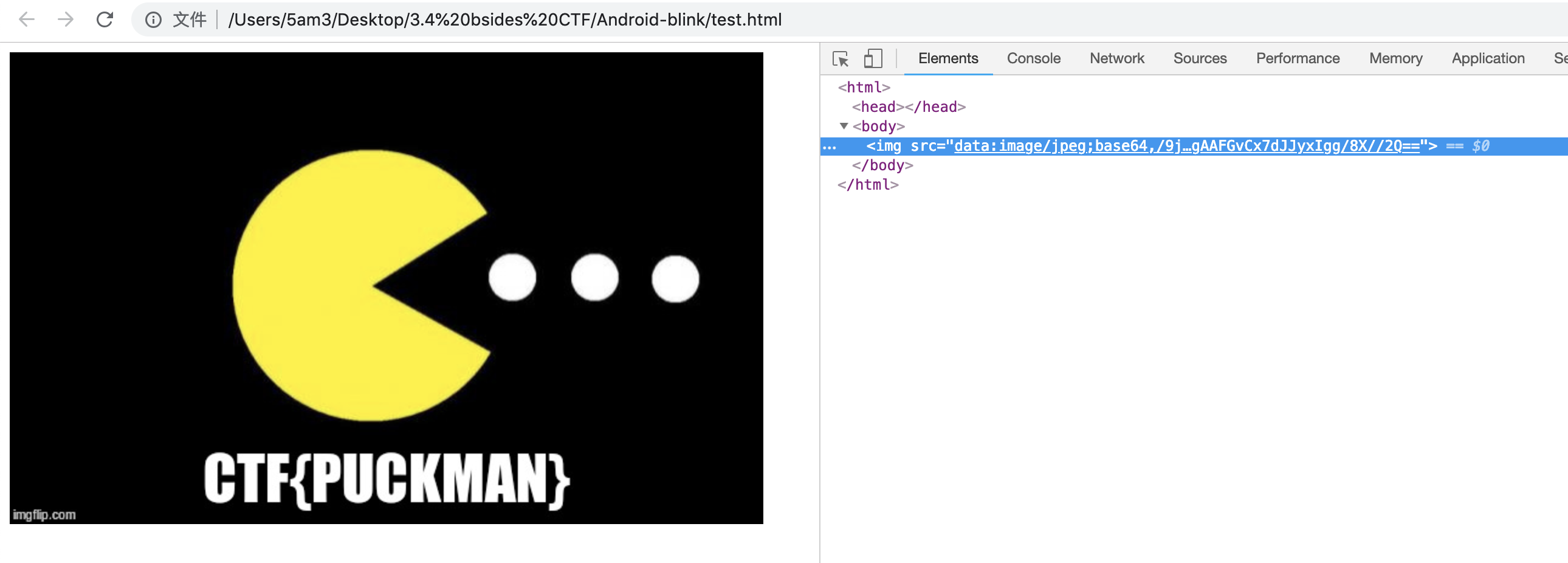
> Get past the Jedi mind trick to find the > flag you are looking for.
> [blink.apk](https://ctf.bsidessf.net/attachment/2076367fc799e89665cf2d674a7590548a6978b68aa18407a028acaa8055a61f)
use dex2jar and convert it to .jar ,then use jd-gui to decompile it,we can find a picture encode with base64 from r2d2.class。
use the html `` tag to decode it.