Tags: baby
Rating:
For a better view check our [githubpage](https://bsempir0x65.github.io/CTF_Writeups/AngstromCTF_2022/#baby3) or [github](https://github.com/bsempir0x65/CTF_Writeups/tree/main/AngstromCTF_2022#baby3) out
So we were given a file that according to the creators does nothing. Instead of real reverse engineering we just started with the strings command to see if the flag is in plain text already present.
```console
└─$ strings chall
/lib64/ld-linux-x86-64.so.2
?;W(
__cxa_finalize
__libc_start_main
__stack_chk_fail
libc.so.6
GLIBC_2.2.5
GLIBC_2.4
GLIBC_2.34
_ITM_deregisterTMCloneTable
__gmon_start__
_ITM_registerTMCloneTable
PTE1
u3UH
actf{emhH <-- whats this hmmm
paidmezeH
rodollarH
stomaketH
hischallH
enge_amoH
gus}
;*3$"
GCC: (GNU) 11.2.0
abi-note.c
__abi_tag
init.c
crtstuff.c
deregister_tm_clones
__do_global_dtors_aux
completed.0
__do_global_dtors_aux_fini_array_entry
frame_dummy
__frame_dummy_init_array_entry
chall.c
__FRAME_END__
_DYNAMIC
__GNU_EH_FRAME_HDR
_GLOBAL_OFFSET_TABLE_
__libc_start_main@GLIBC_2.34
_ITM_deregisterTMCloneTable
_edata
_fini
__stack_chk_fail@GLIBC_2.4
__data_start
__gmon_start__
__dso_handle
_IO_stdin_used
_end
__bss_start
main
__TMC_END__
_ITM_registerTMCloneTable
__cxa_finalize@GLIBC_2.2.5
_init
.symtab
.strtab
.shstrtab
.interp
.note.gnu.property
.note.gnu.build-id
.note.ABI-tag
.gnu.hash
.dynsym
.dynstr
.gnu.version
.gnu.version_r
.rela.dyn
.rela.plt
.init
.text
.fini
.rodata
.eh_frame_hdr
.eh_frame
.init_array
.fini_array
.dynamic
.got
.got.plt
.data
.bss
.comment
```
As you can see we were already lucky. We just needed to put these together and voila we had the flag actf{emhpaidmezerodollarstomakethischallenge_amogus}.
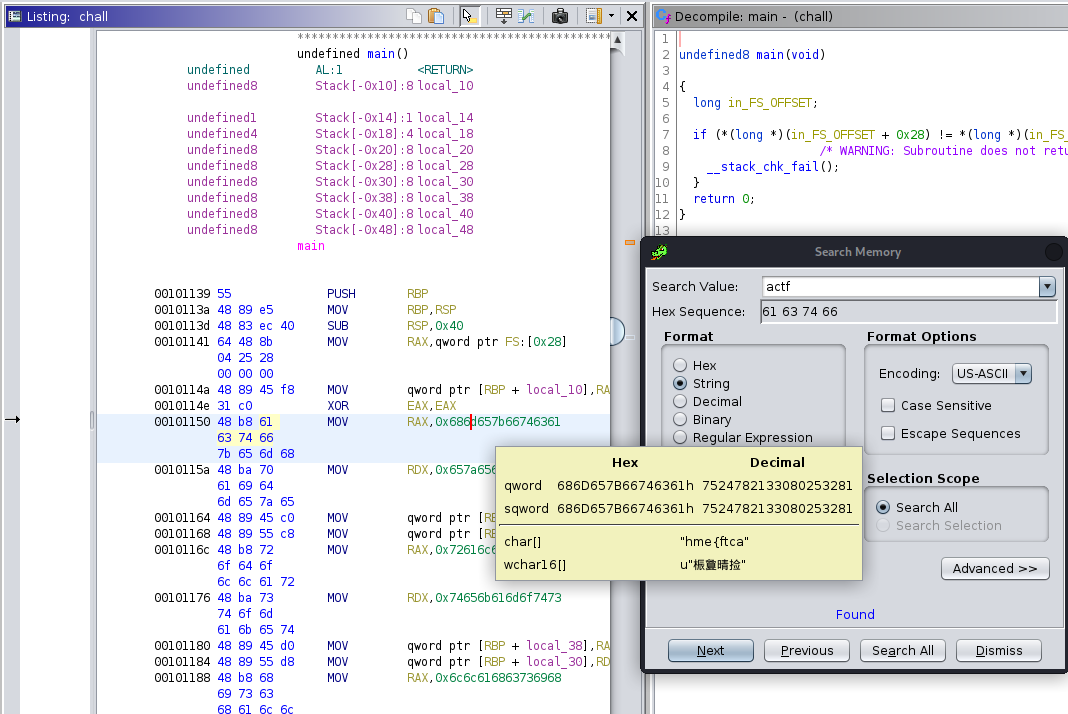
So this way was a bit to easy so we wanted to understand what happens and actually nothing happens. The program just loads the flag into the memory and then exits. As you can see here: