Tags: web
Rating: 5.0
Let's have a look at the challenge description.
> A junior recently started doing PHP, and makes some random shit. He uses gedit as his go-to editor with a black theme thinking it was sublime.
So he made this login portal, I am sure he must have left something out. Why don't you give it a try?
First thing that comes to mind after reading this is, there should be some vulnerability/exploit gedit/PHP related. After reading about gedit a little bit, I came to know that it autosaves files with a `~` at end, example: `index.php~`. This can be used to pull source code / files from the server.
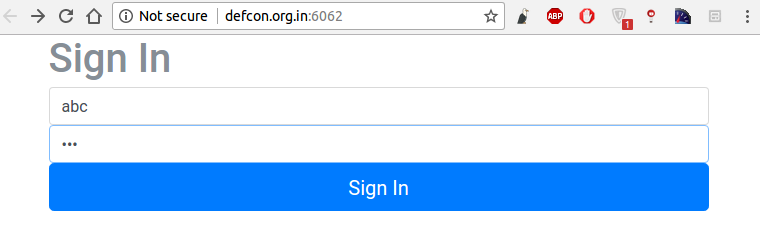
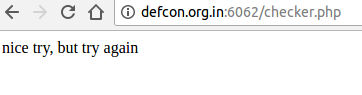
On the website link (http://defcon.org.in:6062) provided in the challenge, after trying some guess username and password combination, it is observed that the data is passed to `checker.php` to verify the credentials. (if image not rendering, click open image in new tab and authenticate)
So, I just change the url to http://defcon.org.in:6062/checker.php~ and Voila! I've downloaded the checker.php file and now, have the source code that checks my credentials. Lets have a look at `checker.php~`
```
<html>
<head></head>
<body>
</body>
</html>
```
Looking at if statement in the file, two things:
- x == y returns true if x and y evaluate to same thing irrespective of type
- x !== y returns true if x and y are not equal, or they are of not same type
Both above conditions need to be fulfilled so that I can get flag.
I quickly went on with username: "100" and password: 100 but didn't work :D ($\_POST handles everything as string by default). After thinking sometime, I found a workaround. `Username: 100, Password: 1e2`. Now both have different types but get evaluated to same value, thus satisfying both conditions. Click on Sign In, and here we go!
`congratulations the flag is d4rk{l0l_g3dit_m4ster_roxx}c0de`