Rating:
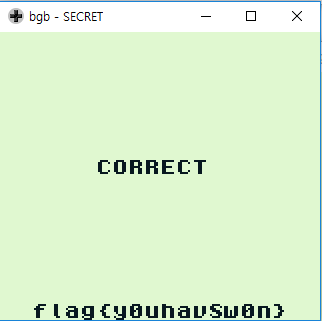
Given a secret.gb file that can be run as a gameboy emulator.
Because of the reversing problem, we used the bgb emulator to debug.
Once "Password:" is displayed and the Enter key is pressed, the INCORRECT string is displayed.
To solve the problem, we decided to search for the CORRECT string.
This string is located at 0x0744. The instruction to this location is at 0x0721 as follows.
```
ROM:0721 jr nz, unk_743
```
You can see that the function starts at 0x0685 when you follow the function linked to it.
```
ROM:0685 ld hl, 0C0D1h
ROM:0688 ld a, (hl)
ROM:0689 cp 10h
ROM:068B jp nc, loc_6C7
ROM:068E ld a, 0A0h ; '
ROM:0690 add a, (hl)
ROM:0691 ld c, a
ROM:0692 ld a, 0C0h ; '
ROM:0694 adc a, 0
ROM:0696 ld b, a
ROM:0697 ld a, (bc) //[C0A0:C0AF] 의 memory 참조
ROM:0698 ld c, a
ROM:0699 cp 10h //C0A0 + k 가 0x10인가?
ROM:069B jp z, loc_6C0
ROM:069E call sub_762 // print “INCORRECT”
ROM:06A1 ld hl, 71Eh
ROM:06A4 push hl
ROM:06A5 call sub_121E
ROM:06A8 ret pe
ROM:06A9 ld (bc), a
ROM:06AA ld hl, 7D0h
ROM:06AD push hl
ROM:06AE call sub_1585
ROM:06B1 ret pe
ROM:06B2 ld (bc), a
ROM:06B3 call sub_20C
ROM:06B6 ld hl, 0C0D0h
ROM:06B9 ld (hl), 0
ROM:06BB ld e, 0
ROM:06BD jp loc_71B
ROM:06C0 ld hl, 0C0D1h
ROM:06C3 inc (hl)
ROM:06C4 jp loc_685 // k <= 0x10
```
The python pseudo code is as follows.
```
for I in range(0x10):
if [0xc0a0 + I] == 0x10:
counter+=1
if counter == 0x10:
get_flag()
```
Now we refer to the memory in the 0xc0a0 part.
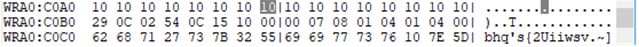
Now I see that every character I type is stored in 0x1, 0x2, 0x4, 0x8, 0x10. For example, if you enter "AAAAAAAAAAAAAAAA", the memory will be 101010101010 ... 10. You can enter a total of 16 characters, and all of these letters can be used to obtain a flag.
In this situation, you can see that c0a0: c0af changes to another number when you breakpoint 0x0685. The numbers you entered are moved to c0b0: c0bf. At this time, I thought of a black box and tried to put all the inputs that could be put into the gameboy.
It will be Up, down, left, and right keys, a, b, select key. Fortunately, there is a one-to-one correspondence between the k-th input and the value of c0a0 + k.
Finally, you can get the flag by putting "04 04 10 40 08 02 02 20 01 08 01 20 01 20 10 20" in the memory of c0a0 - c0af position.